[February-2023]Exam Pass 100%!Braindump2go 300-620 Exam Dumps 300-620 136Q Instant Download[Q95-Q135]
February/2023 Latest Braindump2go 300-620 Exam Dumps with PDF and VCE Free Updated Today! Following are some new Braindump2go 300-620 Real Exam Questions! QUESTION 95
A user needs full read-only visibility into an ACI fabric. Which predefined security domain can be used to enable such visibility? A. common
B. all
C. infra
D. fabric Answer: B QUESTION 96
Out of the following switches, which are spine platforms that support ACI Multi-Site? (Choose two.) A. Nexus 93180YC-EX
B. Nexus 9364C
C. Nexus 9736C-FX line card
D. Nexus 9396PX Answer: BC QUESTION 97
In-band is currently configured and used to manage the Cisco ACI fabric. The requirement is for leaf and spine switches to use out-of-band management for NTP protocol.
Which action accomplishes this goal? A. Select Out-of-Band as Management EPG in the default DateTimePolicy.
B. Create an Override Policy with NTP Out-of-Band for leaf and spine switches.
C. Change the interface used for APIC external connectivity to ooband.
D. Add a new filter to the utilized Out-of-Band-Contract to allow NTP protocol. Answer: A
Explanation:
https://www.cisco.com/c/en/us/support/docs/cloud-systems-management/application-policy-infrastructure-controller-apic/200128-Configuring-NTP-in-ACI-Fabric-Solution.html QUESTION 98
An administrator must migrate the vSphere Management VMkernel of all ESXi hosts in the production cluster from the standard default virtual switch to a VDS that is integrated with APIC in a VMM domain.
Which action must be completed in this scenario? A. The Management VMkernel EPG resolution must be set to Pre-Provosion.
B. The administrator must create an in-band VMM Management EPG before performing the migration.
C. The administrator must set the Management VMkernel BD resolution immediacy to On-Demand.
D. The VMkernel Management BD must be located under the Management Tenant. Answer: A QUESTION 99
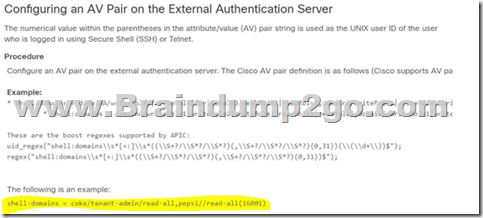
A customer implements RBAC on a Cisco APIC using a Windows RADIUS server that is configured with network control policies. The APIC is as follows:
- Tenant = TenantX
- Security Domain = Tenantx-SD
- User = X
The customer requires User X to have access to TenantX only, without any extra privilege in the Cisco ACI fabric domain.
Which Cisco AV pair must be implemented on the RADIUS server to meet these requirement? A. shell:domains = TenantX-SD/fabric-admin/,common//read-all
B. shell:domains = TenantX-SD/tenant-admin
C. shell:domains = TenantX-SD/tenant-ext-admin/,common//read-all
D. shell:domains = TenantX-SD/tenant-admin/,common//read-all Answer: D
Explanation:
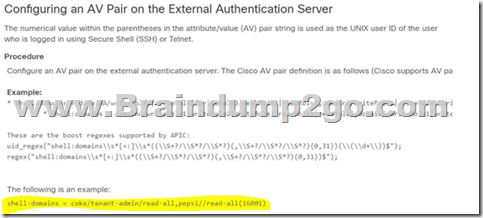
https://www.cisco.com/c/en/us/td/docs/switches/datacenter/aci/apic/sw/2-x/Security_config/b_Cisco_APIC_Security_Guide/b_Cisco_APIC_Security_Guide_chapter_0100.html QUESTION 101
An engineer must create a backup of the Cisco ACI fabric for disaster recovery purposes. The backup must be transferred over a secure and encrypted transport. The backup file must contain all user and password related information. The engineer also wants to process and confirm the backup file validity by using a Python script. This requires the data structure to have a format similar to a Python dictionary. Which configuration set must be used to meet these requirements? A. Under the Create Remote location settings, select Protocol: FTP
Under the Export policy, select
- Format: XML
- Modify Global AES Encryption Settings: Enabled
B. Under the Create Remote location settings, select Protocol: FTP
Under the Export policy, select
- Format: XML
- Modify Global AES Encryption Settings: Disabled
C. Under the Create Remote location settings, select Protocol: SCP
Under the Export policy, select
- Format: JSON
- Modify Global AES Encryption Settings: Disabled
D. Under the Create Remote location settings, select Protocol: SCP
Under the Export policy, select
- Format: JSON
- Modify Global AES Encryption Settings: Enabled Answer: D QUESTION 102
The Application team reports that a previously existing port group has disappeared from vCenter. An engineer confirms that the VM domain association for the EPG is no longer present.
Which action determines which user is responsible for the change? A. Check the EPG audit logs for the "deletion" action and compare the affected object and user.
B. Evaluate the potential faults that are raised for that EPG.
C. Examine the health score and drill down to an object that affects the EPG combined score.
D. Inspect the server logs to see who was logging in to the APIC during the last few hours. Answer: B QUESTION 103
An application team tells the Cisco ACI network administrator that it wants to monitor the statistics of the unicast and BUM traffic that are seen in a certain EPG. Which statement describes the collection statistics? A. All EPGs in the Cisco ACI tenant object must be enabled for statistics to be collected.
B. Cisco ACI does not capture statistics at the EPG level. Only statistics that pass through ACI contracts can be monitored.
C. EPG statistics can be collected only for VMM domains. If a physical domain exists, statistics are not collected.
D. The collection of statistics is enabled on the EPG level by enabling the statistics for unicast and BUM traffic. Answer: D
Explanation:

https://www.cisco.com/c/en/us/td/docs/switches/datacenter/aci/apic/sw/1-x/Operating_ACI/guide/b_Cisco_Operating_ACI/b_Cisco_Operating_ACI_chapter_01011.html QUESTION 104
All workloads in VLAN 1001 have been migrated into EPG-1001. The requirement is to move the gateway address for VLAN 1001 from the core outside the Cisco ACI fabric into the Cisco ACI fabric. The endpoints in EPG-1001 must route traffic to endpoints in other EPGs and minimize flooded traffic in the fabric.
Which configuration set is needed on the bridge domain to meet these requirements? A. Disable ARP Flood
Disable Limn Endpoint Learning
B. Enable Hardware Proxy Enable Unicas! Routing
C. Disable Local IP Learning Limit Disable Unicast Routing
D. Enable Flood
Enable Unicast Routing Answer: B QUESTION 105
An engineer is in the process of discovering a new Cisco ACI fabric consisting of two spines and four leaf switches. The discovery of leaf 1 has just been completed.
Which two nodes are expected to be discovered next? (Choose two.) A. spine 1
B. leaf 4
C. spine 2
D. leaf 3
E. leaf 2 Answer: AC QUESTION 106
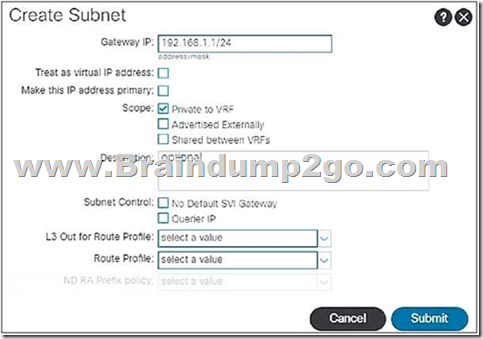
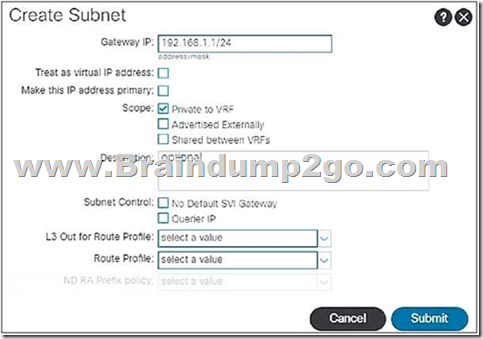
When the subnet is configured on a bridge domain, on which physical devices is the gateway IP address configured?
A. all leaf switches and all spine nodes
B. only spine switches where the bridge domain of the tenant is present
C. only leaf switches where the bridge domain of the tenant is present
D. all border leaf nodes where the bridge domain of the tenant is present Answer: C
Explanation:
http://www.netdesignarena.com/index.php/2016/06/16/aci-tenant-building-blocks-forwarding-logic/
https://www.cisco.com/c/en/us/td/docs/switches/datacenter/aci/apic/sw/1-x/Operating_ACI/guide/b_Cisco_Operating_ACI/b_Cisco_Operating_ACI_chapter_0111.html
 QUESTION 107
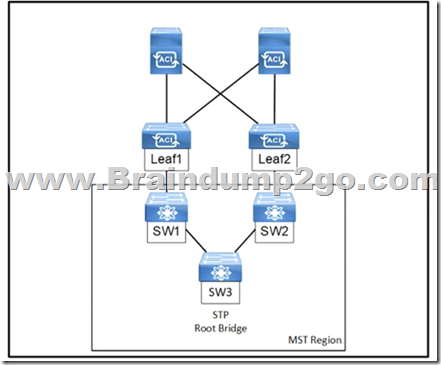
Refer to the exhibit, An engineer is deploying a Cisco ACI environment but experiences a STP loop between switch1 and switch2. Which configuration step is needed to break the STP loop?
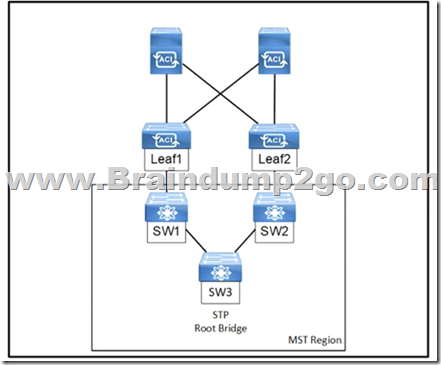 A. Configure the STP instance to VLAN mapping under the switch STP policy.
B. Configure a Layer 2 external bridged network on the interfaces facing the MST switches.
C. Enable the native VLAN on the interfaces facing the MST switches using static pons in a dedicated EPG.
D. Enable BPDU filter under the STP interface policy on the Interfaces lacing the MST switches. Answer: C QUESTION 108
A Solutions Architect is asked to design two data centers based on Cisco ACI technology that can extend L2/L3, VXLAN, and network policy across locations. ACI Multi-Pod has been selected. Which two requirements must be considered in this design? (Choose two.) A. ACI underlay protocols, i.e. COOP, IS-IS and MP-BGP, spans across pods. Create QoS policies to make sure those protocols have higher priority.
B. A single APIC Cluster is required in a Multi-Pod design. It is important to place the APIC Controllers in different locations in order to maximize redundancy and reliability.
C. ACI Multi-Pod requires an IP Network supporting PIM-Bidir.
D. ACI Multi-Pod does not support Firewall Clusters across Pods. Firewall Clusters should always be local.
E. Multi-Pod requires multiple APIC Controller Clusters, one per pod. Make sure those clusters can communicate to each other through a highly available connection. Answer: BC
Explanation:
Multipod is with only a single APIC cluster - multisite requires multiple clusters.
"The entire network hence runs as a single large fabric from an operational perspective; however, ACI Multi-Pod introduces specific enhancements to isolate as much as possible the failure domains between Pods, contributing to increase the overall design resiliency. This is achieved by running separate instances of fabric control planes (IS-IS, COOP, MP-BGP) across Pods."
https://www.cisco.com/c/en/us/solutions/collateral/data-center-virtualization/application-centric-infrastructure/white-paper-c11-737855.html QUESTION 109
An engineer must perform a Cisco ACI fabric upgrade that minimizes the impact on user traffic and allows only permitted users to perform an upgrade.
Which two configuration steps should be taken to meet these requirements? A. Divide Cisco APIC controllers into two or more maintenance groups.
B. Grant tenant-ext-admin access to a user who performs an upgrade
C. Combine all switches into an upgrade group.
D. Divide switches into two or more maintenance groups.
E. Grant the fabric administrator role to a user who performs an upgrade. Answer: DE QUESTION 110
What do Pods use to allow Pod-to-Pod communication in a Cisco ACI Multi-Pod environment? A. over Layer 3 directly connected back-to-back spines
B. over Layer 3 Out connectivity via border leafs
C. over Layer 3 IPN connectivity via border leafs
D. over Layer 3 IPN connectivity via spines Answer: D
Explanation:
https://www.cisco.com/c/en/us/solutions/collateral/data-center-virtualization/application-centric-infrastructure/white-paper-c11-737855.html QUESTION 111
Which routing protocol is supported between Cisco ACI spines and IPNs in a Cisco ACI Multi-Pod environment? A. OSPF
B. IS-IS
C. BGP
D. EIGRP Answer: A QUESTION 112
An engineer must deploy Cisco ACI across 10 geographically separated data centers. Which ACI site deployment feature enables the engineer to control which bridge domains contain Layer 2 flooding? A. GOLF
B. Multi-Site
C. Multi-Pod
D. Stretched Fabric Answer: B
Explanation:
https://www.cisco.com/c/en/us/td/docs/switches/datacenter/aci/aci_multi-site/sw/2x/fundamentals/Cisco-ACI-Multi-Site-Fundamentals-Guide-211/Cisco-ACI-Multi-Site-Fundamentals-Guide-211_chapter_011.html#id_51188
From the web page, we see that multi-site has control over:
Stretched Bridge Domain with Layer 2 Broadcast Extension. Stretched Bridge Domain with no Layer 2 Broadcast Extension. QUESTION 113
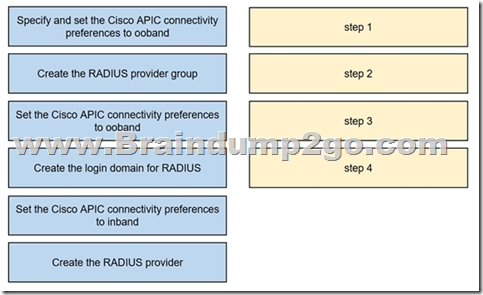
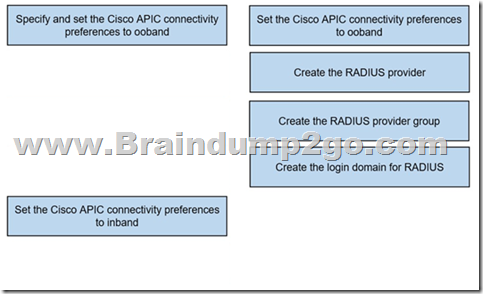
Drag and Drop Question
An engineer must configure RADIUS authentication with Cisco ACI for remote authentication with out-of-band management access. Drag and drop the RADIUS configuration steps from the left into the required implementation order on the right. Not all steps are used.
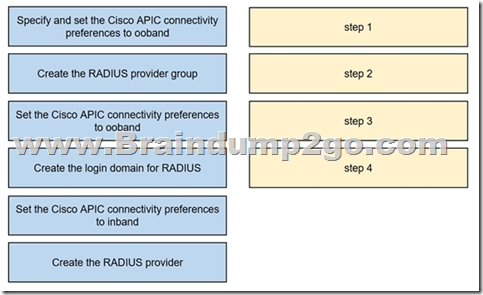
Answer:
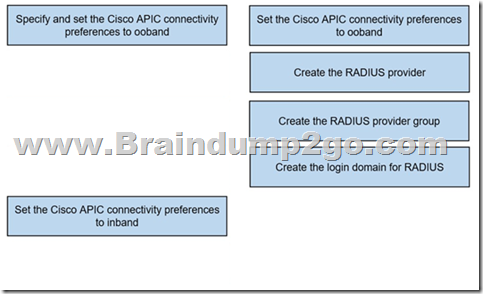
Explanation:
Set OOBAND first, the RADIUS servers are outside!
ACI configuration for RADIUS involves the following three basic steps:
Step 1. Create the desired RADIUS providers.
Step 2. If using ACI versions prior to Release 4 or configuring via the APIC CLI, create a RADIUS provider group.
Step 3. Create a RADIUS login domain. QUESTION 114
Which statements are correct regarding ACI support for BFD? (Choose two.) A. BFD is supported for EIGRP, OSPF, and BGP in ACI.
B. BFD is supported on L3Out loopback interfaces.
C. BFD is supported for BGP prefix peers (dynamic neighbors).
D. BFD is supported on routed interfaces, routed subinterfaces, and SVIs. Answer: AD QUESTION 115
An engineer must advertise a selection of external networks learned from a BGP neighbor into the ACI fabric. Which L3Out subnet configuration option creates an inbound route map for route filtering? A. External Subnets for the External EPG
B. Shared Route Control Subnet
C. Import Route Control Subnet
D. Shared Security Import Subnet Answer: C QUESTION 116
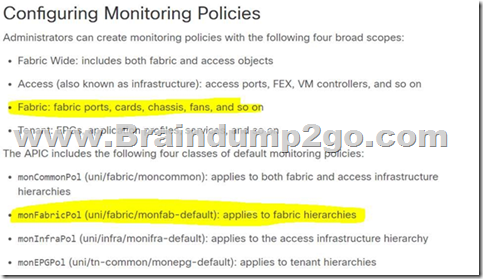
An engineer must set up a Cisco ACI fabric to send Syslog messages related to hardware events, such as chassis line card failures. The messages should be sent to a dedicated Syslog server. Where in the Cisco APIC should the policy be configured to meet this requirement? A. uni/tn-common/monepg-default
B. uni/infra/monifra-default
C. uni/fabric/monfab-default
D. uni/fabric/moncommon Answer: C
Explanation:
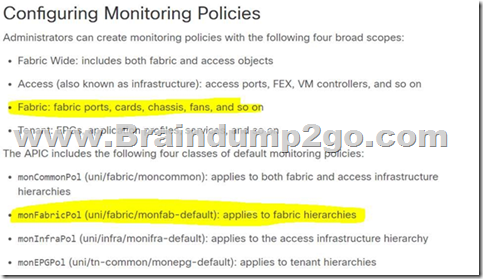
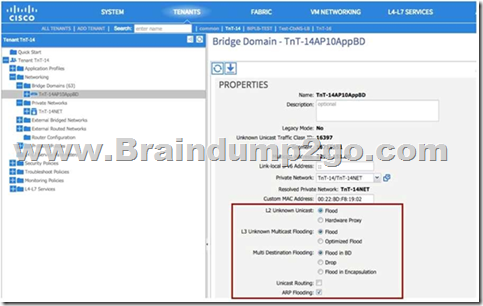
https://www.cisco.com/c/en/us/td/docs/switches/datacenter/aci/apic/sw/4-x/aci-fundamentals/Cisco-ACI-Fundamentals-401/Cisco-ACI-Fundamentals-401_chapter_01100.html QUESTION 117
The existing network and ACI fabric have been connected to support workload migration. Servers will physically terminate at the Cisco ACI, but their gateway must stay in the existing network. The solution needs to adhere to Cisco's best practices. The engineer started configuring the relevant Bridge Domain and needs to complete the configuration. Which group of settings are required to meet these requirements? A. L2 Unknown Unicast: Hardware Proxy
L3 Unknown Multicast Flooding: Flood
Multi Destination Flooding: Flood in BD
ARP Flooding: Enable
B. L2 Unknown Unicast: Flood
L3 Unknown Multicast Flooding: Flood
Multi Destination Flooding: Flood in BD
ARP Flooding: Enable
C. L2 Unknown Unicast: Flood
L3 Unknown Multicast Flooding: Optimize Flood
Multi Destination Flooding: Flood in BD
ARP Flooding: Disable
D. L2 Unknown Unicast: Hardware Proxy
L3 Unknown Multicast Flooding: Optimize Flood
Multi Destination Flooding: Flood in BD
ARP Flooding: Disable Answer: B
Explanation:
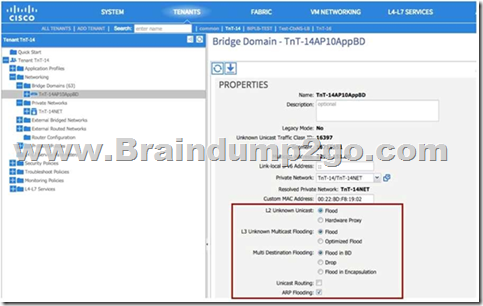
https://www.cisco.com/c/en/us/td/docs/switches/datacenter/aci/apic/sw/migration_guides/migrating_existing_networks_to_aci.html QUESTION 118
An engineer must implement management policy and data plane separation in the Cisco ACI fabric. Which ACI object must be created in Cisco APIC to accomplish this goal? A. Application profile
B. Tenant
C. Contract
D. Bridge domain Answer: B
Explanation:
An ACI tenant is a secure and exclusive virtual computing environment that forms a unit of isolation from a policy perspective but does not represent a private network.
If you investigate further into use cases for tenants in the real world, you will find that tenants are often deployed in order to achieve these two technical controls:
- Administrative separation
- Configuration fault isolation QUESTION 119
An engineer is implementing a Cisco ACI environment that consists of more than 20 servers. Two of the servers support only Cisco Discovery Protocol with no order link discovery protocol. The engineer wants the servers to be discovered automatically by the Cisco ACI fabric when connected. Which action must be taken to meet this requirement? A. Create an override policy that enables Cisco Discovery Protocol after LLDP is enabled in the default policy group.
B. Configure a higher order interface policy that enables Cisco Discovery Protocol for the interface on the desired leaf switch.
C. Configure a lower order policy group that enables Cisco Discovery Protocol for the interface on the desired leaf switch.
D. Create an interface profile for the interface that disables LLDP on the desired switch that is referenced by the interface policy group. Answer: A
Explanation:
A leaf interface override policy allows interfaces that have interface policy group assignments to apply an alternate interface policy group.
Imagine that a group of ports have been configured on Node 101, using a specific interface policy group.
One of the interfaces connects to a firewall, and security policies dictate that LLDP and CDP toward the firewall need to be disabled on all firewall-facing interfaces.
It might be impossible to modify the interface policy group associated with the port because it might be part of a port block.
In this case, a leaf interface override can be used to assign an alternative interface policy group to the port of interest. QUESTION 120
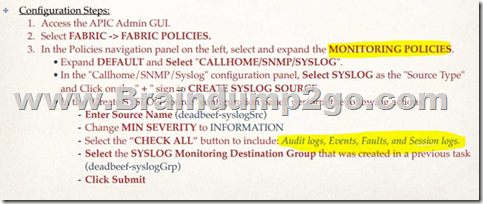
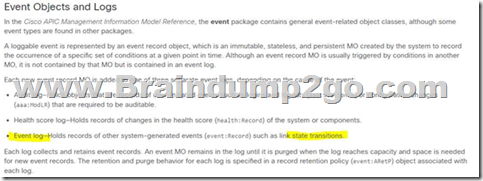
An engineer wants to monitor all configuration changes, threshold crossing, and link-state transitions in a Cisco ACI fabric. Which action must be taken to receive the required messages? A. Add Faults and Events to the monitor policy.
B. Add Session Logs and Audit Logs to the monitor policy.
C. Include Audit Logs and Events in the Syslog source policy.
D. Include Events and Session Logs in the Syslog source policy. Answer: B
Explanation:
After searching, there is nothing called "syslog source policy" in ACI. Syslog source policy exists in UCS Central. The choices now are on "Monitoring Policy" that exits on A and C.
https://community.cisco.com/legacyfs/online/attachments/blog/technote-aci-syslog_external- latest.pdf
https://www.cisco.com/c/en/us/td/docs/switches/datacenter/aci/apic/sw/all/faults/guide/b_APIC_F aults_Errors/b_IFC_Faults_Errors_chapter_010.html
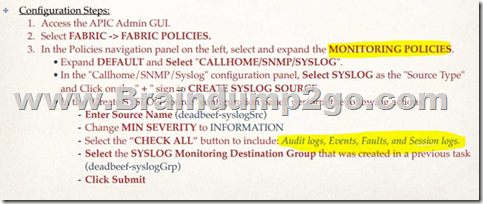
 QUESTION 121
An organization has encountered many STP-related issues in the past due to failed hardware components. They are in the process of long-term migration to a newly deployed ACI fabric. Senior engineers are worried that spanning-tree loops in the existing network may be extended to the ACI fabric. Which feature must be enabled on the ACI leaf ports to protect the fabric from spanning-tree loops? A. BPDU Guard
B. per-VLAN MCP
C. Storm Control
D. BPDU Filter Answer: B
Explanation:
A Layer 2 loop does not impact the stability of an ACI fabric because ACI can broadcast traffic at line rate with little need to process the individual packets.
Layer 2 loops, however, can impact the ability of endpoints to process important traffic.
For this reason, mechanisms are needed to detect loops resulting from miscabling and misconfiguration.
One of the protocols ACI uses to detect such externally generated Layer 2 loops is MisCabling Protocol (MCP).
MCP is disabled in ACI by default. To enable MCP, you must first enable MCP globally and then ensure that it is also enabled at the interface policy level.
As part of the global enablement of MCP, you define a key that ACI includes in MCP packets sent out on access ports.
If ACI later receives an MCP packet with the same key on any other port, it knows that there is a Layer 2 loop in the topology.
In response, ACI can either attempt to mitigate the loop by disabling the port on which the MCP protocol data unit was received or
it can generate a system message to notify administrators of the issue.
Reference:
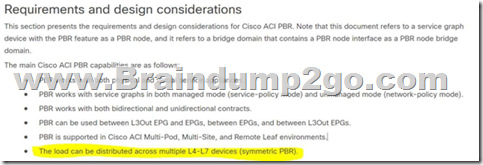
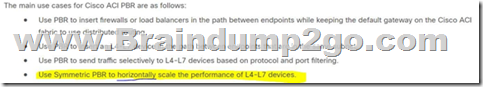
https://www.cisco.com/c/en/us/td/docs/switches/datacenter/aci/apic/sw/4-x/aci-fundamentals/Cisco-ACI-Fundamentals-401/Cisco-ACI-Fundamentals-401_chapter_0101.html#concept_706016DC62404574B77A5A4B3AD3C905 QUESTION 122
A network engineer must design a method to allow the Cisco ACI to redirect traffic to the firewalls. Only traffic that matches specific L4-L7 policy rules should be redirected. The load must be distributed across multiple firewalls to scale the performance horizontally. Which action must be taken to meet these requirements? A. Configure ACI Service Graph with Unidirectional PBR.
B. Implement ACI Service Graph with GIPo.
C. Implement ACI Service Graph Two Nodes with GIPo.
D. Configure ACI Service Graph with Symmetric PBR. Answer: D
Explanation:
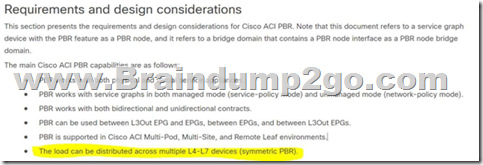
https://www.cisco.com/c/en/us/solutions/collateral/data-center-virtualization/application-centric-infrastructure/white-paper-c11-739971.html QUESTION 123
An engineer created two interface protocol policies called Pol_CDP40275332 and Pol_LLDP46783451.
The policies must be used together in a single policy. Which ACI object must be used? A. interface policy group
B. switch policy group
C. switch profile
D. interface profile Answer: A
Explanation:
LLDP and CDP can be used on the same interface.
A CDP policy will be created like this:
Fabric > Access Policies > Policies > Interface > CDP Interface > <create Your policy>
A LLDP policy will be created like this:
Fabric > Access Policies > Policies > Interface > LLDP Interface > <create Your policy>
Both policies are independant to each other and can be applied within an Interface Policy Group
Fabric > Access Policies > Interfaces > Leaf Interfaces > Policy Group > Leaf Access Port > <Your policy here > > <set a CDP and a LLDP policy within Your interface policy group>
An interface profile will be used to create an interface selector.
The interface selector has physical ports and also calls Your interface policy group.
Reference: https://sandboxapicdc.cisco.com QUESTION 124
What is the minimum number of APICs does Cisco recommend to deploy in a production cluster? A. 1
B. 3
C. 4
D. 5 Answer: B QUESTION 125
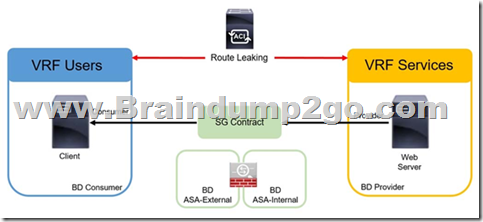
Refer to the exhibit. An engineer must implement the inter-tenant service graph. Which set of actions must be taken to accomplish this goal?
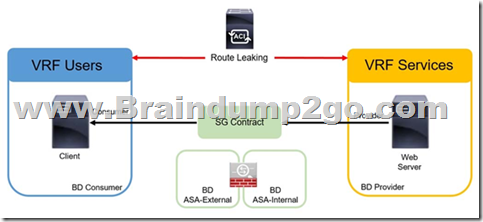 A. - Define the contract in the provider tenant and export it to the consumer tenant.
- Define the L4-L7 device, service graph template, and ASA bridge domains in the provider tenant.
B. - Define the contract in the provider tenant and export it to the consumer tenant.
- Define the L4-L7 device and service graph template in the provider tenant and the ASA bridge domains in the consumer tenant.
C. - Define the contract in the provider tenant and export it to the provider tenant.
- Define the L4-L7 device and service graph template in the provider tenant and the ASA bridge domains in the consumer tenant.
D. - Define the contract in the provider tenant and export it to the provider tenant.
- Define the L4-L7 device, service graph template, and ASA bridge domains in the consumer tenant. Answer: A QUESTION 126
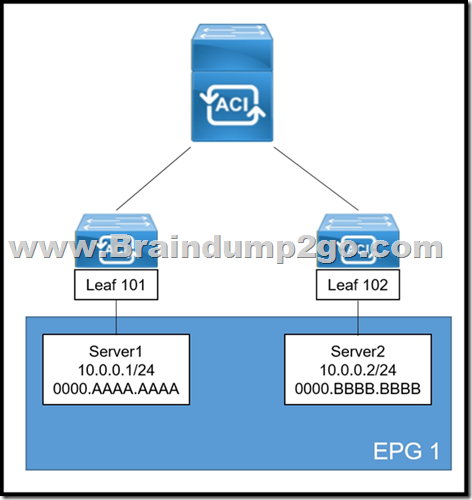
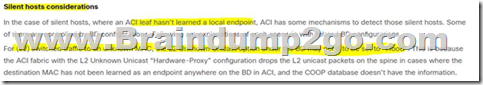
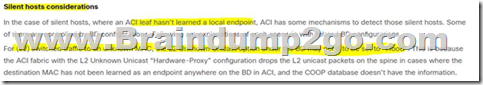
Refer to the exhibit. A systems engineer is implementing the Cisco ACI fabric. However, the Server2 information is missing from the Leaf 101 endpoint table and the COOP database of the spine. The requirement is for the bridge domain configuration to enforce the ACI fabric to forward the unicast packets generated by Server1 destined to Server2. Which action must be taken to meet these requirements?
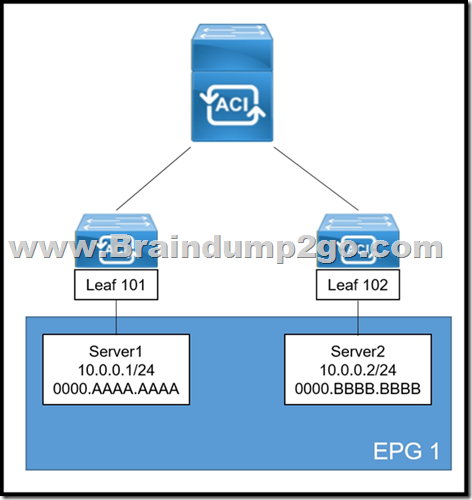 A. Enable ARP Flooding
B. Set L2 Unknown Unicast to Flood
C. Set IP Data-Plane Learning to No
D. Enable Unicast Routing Answer: B
Explanation:
Both servers are in the same subnet. ARP flooding is out if we read the article in the link. Also unicast routing is not needed.
https://www.cisco.com/c/en/us/solutions/collateral/data-center-virtualization/application-centric-infrastructure/white-paper-c11-739989.html
 QUESTION 127
An engineer must allow multiple external networks to communicate with internal ACI subnets. Which action should the engineer take to assign the prefix to the class ID of the external Endpoint Group? A. Enable the Export Route Control Subnet for the External Endpoint Group flag.
B. Enable an L3Out with Shared Route Control Subnet.
C. Configure subnets with the External Subnets for External EPG flag enabled.
D. Configure subnets with the Import Route Control Subnet flag enabled. Answer: C
Explanation:

https://www.cisco.com/c/en/us/td/docs/switches/datacenter/aci/apic/sw/1- x/ACI_Best_Practices/b_ACI_Best_Practices/b_ACI_Best_Practices_chapter_01001.html QUESTION 128
An engineer must ensure that Cisco ACI flushes the appropriate endpoints when a topology change notification message is received in an MST domain.
Which three steps are required to accomplish this goal? (Choose three.) A. Enable the BPDU interface controls under the spanning tree interface policy.
B. Configure a new STP interface policy.
C. Bind the spanning tree policy to the switch policy group.
D. Associate the STP interface policy to the appropriate interface policy group.
E. Create a new region policy under the spanning tree policy.
F. Map VLAN range to MAT instance number. Answer: CEF
Explanation:
Create a new region policy under the spanning tree policy.
Map VLAN range to MST instance number.
Bind the spanning tree policy to the switch policy group.
These steps allow the ACI system to understand MST BPDUs. ACI can now flush the appropriate endpoints when a TCN message is received in an MST domain. QUESTION 129
A Cisco ACI bridge domain and VRF are configured with a default data-plane learning configuration. Which two endpoint attributes are programmed in the leaf switch when receiving traffic? (Choose two.) A. Remote MAC, IP
B. Remote Subnet
C. Local IP, not MAC
D. Local MAC, IP
E. Local Subnet
F. Remote IP Answer: AD QUESTION 130
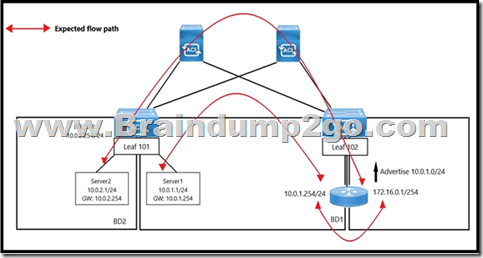
Refer to the exhibit. An engineer wants to initiate an ICMP ping from Server1 to Server2. The requirement is for the BD1 to enforce ICMP replies that follow the expected path. The packets must be prevented from taking the direct path from Leaf1 to Server1. Which action must be taken on BD1 to meet these requirements?
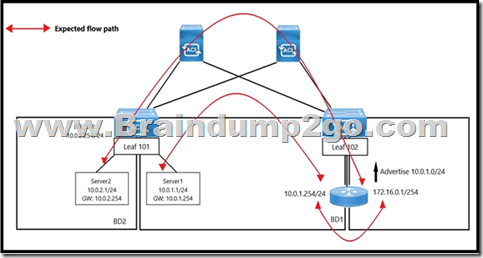 A. Set L2 Unknown Unicast to Flood.
B. Set L2 Unknown Unicast to Hardware Proxy.
C. Disable Unicast Routing.
D. Enable ARP Flooding. Answer: B QUESTION 131
An engineer must configure a group of servers with a contract that uses TCP port 80. The EGP that contains the web servers requires an external Layer 3 cloud to initiate communication. Which action must be taken to meet these requirements? A. Configure the EGP as a provider and L3 out as consumer of the contract.
B. Configure OSPF to exchange routes between the L3 out and EGP.
C. Configure a taboo contract and apply it to the EPG.
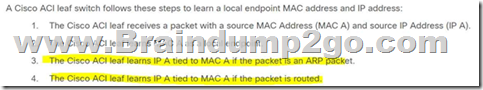
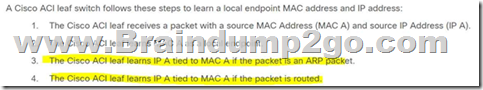
D. Configure the EPG as a consumer and L3 out as a provider of the contract. Answer: A QUESTION 132
The unicast routing feature is enabled on the bridge domain. Which two conditions enable the Cisco ACI leaf to learn a source IP as a local endpoint? (Choose two.) A. Through Ethernet traffic received in a bridge domain.
B. IP traffic routed through an SVI.
C. Through VXLAN traffic received on the uplink.
D. IP traffic routed through a Layer 3 Out.
E. Through ARP received on an SVI. Answer: BE
Explanation:
https://www.cisco.com/c/en/us/solutions/collateral/data-center-virtualization/application-centric-infrastructure/white-paper-c11-739989.html
 QUESTION 133
When does the Cisco ACI leaf learn a source IP or MAC as a remote endpoint? A. When VXLAN traffic arrives on a leaf fabric port from the spine and outer source IP is in the Layer 3 Out EPG subnet range.
B. When VXLAN traffic arrives on a leaf fabric port from the spine and outer source IP is in the bridge domain subnets range.
C. When VXLAN traffic arrives on a leaf fabric port from the spine and inner source IP is in the Layer 3 Out EPG subnet range.
D. When VXLAN traffic arrives on a leaf fabric port from the spine and inner source IP is in the bridge domain subnets range. Answer: D QUESTION 134
The company ESXi infrastructure is hosted on the Cisco UCS-B Blade Servers. The company decided to take advantage of ACI VMM integration to enable consistent enforcement of policies across virtual and physical workloads. The requirement is to prevent the packet loss between the distributed virtual switch and the ACI fabric. Which setting must be implemented on a vSwitch policy to accomplish this goal? A. Static Channel
B. MAC Pinning
C. LACP
D. LLDP Answer: B
Explanation:
Configure the vSwitch Policies on APIC for UCS B
... ... ...
Along with this, the only supported load balancing mechanism when UCS B series is used is Route Based on Originating Virtual Port.
If you configure a mac-pinning policy, it programs the port groups to use this mechanism. This is very important in order to prevent packet loss.
Reference:
https://www.cisco.com/c/en/us/support/docs/cloud-systems-management/application-policy-infrastructure-controller-apic/118965-config-vmm-aci-ucs-00.html QUESTION 135
An engineer is configuring ACI VMM domain integration with Cisco UCS-B Series.
Which type of port channel policy must be configured in the vSwitch policy? A. LACP Active
B. MAC Pinning
C. LACP Passive
D. MAC Pinning-Physical-NIC-load Answer: B
Explanation:
Configure the vSwitch Policies on APIC for UCS B
... ... ...
Along with this, the only supported load balancing mechanism when UCS B series is used is Route Based on Originating Virtual Port.
If you configure a mac-pinning policy, it programs the port groups to use this mechanism. This is very important in order to prevent packet loss.
Reference:
https://www.cisco.com/c/en/us/support/docs/cloud-systems-management/application-policy-infrastructure-controller-apic/118965-config-vmm-aci-ucs-00.html
Resources From:1.2023 Latest Braindump2go 300-620 Exam Dumps (PDF & VCE) Free Share:
https://www.braindump2go.com/300-620.html 2.2023 Latest Braindump2go 300-620 PDF and 300-620 VCE Dumps Free Share:
https://drive.google.com/drive/folders/1hx8JLBTuYBZKFq5qp0Ug2jvJSDvWZrd9?usp=sharing Free Resources from Braindump2go,We Devoted to Helping You 100% Pass All Exams!
|