Braindump2go Full Money Back Promise for New Released Microsoft 70-689 Exam 100% Pass Without Doubt! (181-190)
Instant Download 70-689 PDF Files! New Updated 299 Exam Questions and Answers help 100% Exam Pass! 70-689 Certification Get Quickly! Vendor: Microsoft
Exam Code: 70-689
Exam Name: Microsoft Upgrading Your Skills to MCSA Windows 8.1 
QUESTION 181
You are a systems administrator for Contoso; Ltd.
All client computers run Windows 8 and are members of the contoso.com Active Directory domain.
Users log on to their computers by using domain user accounts.
Contoso develops an internal line of business (LOB) Windows Store app.
You want to deploy the LOB app to the client computers and configure the app to access various resources in the domain.
You need to enable all users to run the LOB app and access the required resources from the LOB app.
What should you do? A. Certify the LOB app with Windows Store.
Ask users to log on to their computers by using a Microsoft Account.
Install the LOB app from Windows Store.
Ask users to log off, and then log back on in by using their domain accounts.
B. Restart each computer by using WinPE.
From WinPE, copy all of the LOB app executable files in the Program Files folder.
Restart into Windows 8 and ask users to log on by using their domain accounts.
C. Use the DISM utility to include the LOB app in a new Windows 8 image.
Reimage the computers with the new image.
Join the computers to a new workgroup.
Ask each user to log on to the computer by using a new Microsoft Account that ends with
@contoso.com.
D. Configure the Allow all trusted apps to install policy settings for all computers.
Ask users to log on by using their domain accounts, and then execute a PowerShell script
that includes the add-appxpackage cmdlet. Answer: A QUESTION 182
You administer a company network that includes a wireless network infrastructure and computers that run Windows 8 Enterprise.
You are planning to add a guest wireless network.
You need to collect information about nearby wireless networks, including their encryption methods.
Which command should you include in the batch file? A. Netsh wlan set autoconfig enabled=no interface="Wireless Network Connection"
B. ipconfig /allcompartments
C. Get-WmiObject win32_networkadapterconfiguration -Filter 'ipenabled = "true"'
D. netsh wlan show networks
E. netsh wlan show hostednetwork
F. netstat -a Answer: D QUESTION 183
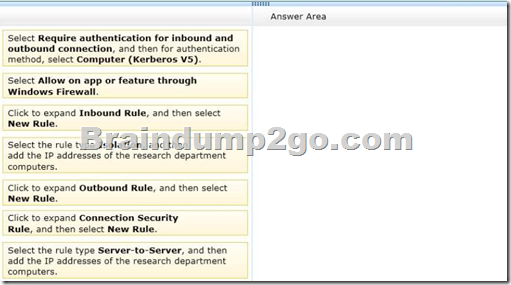
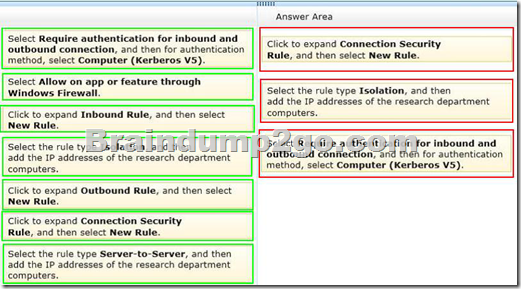
Drag and Drop Questions
You administer desktop computers that run Windows 8 Enterprise and are members of an Active Directory domain.
A new security policy states that all traffic between computers in the research department must be encrypted and authenticated by using Kerberos V5.
You need to configure the requested traffic authentication settings by using Windows Firewall with Advanced Settings.
Which three actions should you perform in sequence? (To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.) 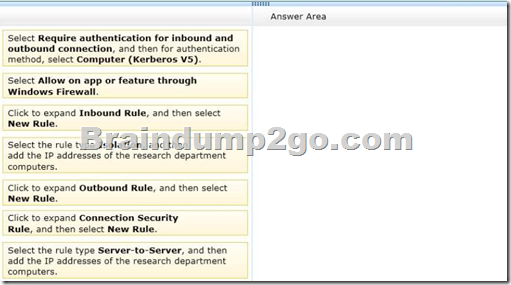
Answer: 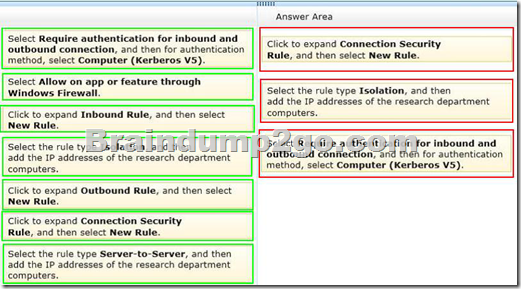
Explanation:
A connection security rule forces two peer computers to authenticate before they can establish a connection and to secure information transmitted between the two computers.
Windows Firewall with Advanced Security uses IPsec to enforce these rules.
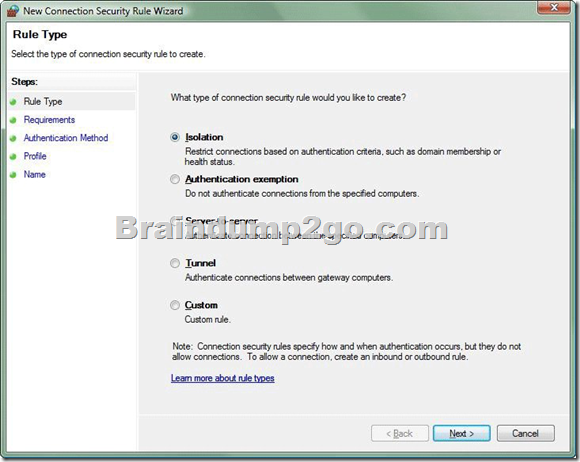
To create a connection security rule
1. In Windows Firewall with Advanced Security, in the console tree, click Connection Security Rules.
2. In the Actions list, click New Rule.
The Rule Type page, shown in the Figure below, allows you to select the type of rule you want to create. Select a type, and use the wizard to configure the new rule according to the information in the following sections. 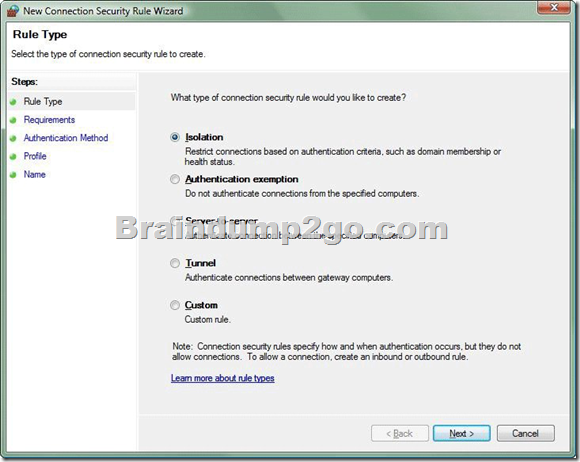
Isolation
An isolation rule isolates computers by restricting inbound connections based on credentials, such as domain membership or compliance with policies that define the required software and system configurations. Isolation rules allow you to implement a server or domain isolation strategy. When you create an isolation rule, you will see the following wizard pages:
Requirements. You can choose when authentication is required:
- Request authentication for inbound and outbound connections
- Require authentication for inbound connections and request authentication for outbound connections
- Require authentication for inbound and outbound connections
- Authentication Method.
You can select from the following authentication methods:
Default. This selection uses the current computer default selections specified on the IPsec Settings tab of the Windows Firewall Properties page.
Computer and user (Kerberos V5). This method uses both computer-and user-based Kerberos V5 authentication to restrict connections to domain-joined users and computers.
User authentication, and therefore this method, is compatible only with computers running Windows Vista and later.
Computer (Kerberos V5). This method uses Kerberos V5 authentication to restrict connections to domain-joined computers. This method is compatible with computers running Windows 2000 or later.
Advanced. This setting allows you to designate multiple authentication methods, such as computer certificate, NTLMv2, and preshared key.
- Profile. Choose the profiles (Domain, Public, and Private) to which the rule applies.
- Name. Name the rule and type an optional description.
Reference: Creating Connection Security Rules QUESTION 184
You support desktop computers and tablets that run Windows 8 Enterprise.
All of the computers are able to connect to your company network from the Internet by using DirectAccess.
Your company wants to deploy a new application to the tablets.
The deployment solution must meet the following requirements:
- The application is stored locally on the tablets.
- Access to the application is protected with extra logon credentials, in addition to a standard domain account used by users.
- The application utilizes the least amount of network bandwidth.
- The application must maintain access to the current desktop.
You need to deploy the new application to the tablets.
What should you do? A. Deploy the application as an Application Virtualization (App-V) package.
Install the App-V 4.6 client on the tablets.
B. Deploy the application as a published application on the Remote Desktop server.
Create a Remote Desktop connection on the tablets.
C. Install the application on a local drive on the tablets.
D. Install the application in a Windows To Go workspace.
E. Install Hyper-V on tablets.
Install the application on a virtual machine.
F. Publish the application to Windows Store.
G. Install the application within a separate Windows 8 installation in a virtual hard disk (VHD) file.
Configure the tablets with dual boot.
H. Install the application within a separate Windows 8 installation in a VHDX file.
Configure tablets with dual boot. Answer: E
Explanation:
http://technet.microsoft.com/en-us/library/hh857623.aspx 1 QUESTION 185
You support desktop computers and tablets that run Windows 8.
Domain joined computers are able to connect to your company network from the Internet by using DirectAccess.
Your company wants to deploy a new application to the tablets.
The deployment solution must meet the following requirements:
- The application is installed locally on the tablets.
- The application installation is hosted in a public cloud.
- The installation must support Windows RT.
You need to deploy the new application to the tablets.
What should you do? A. Deploy the application as an Application Virtualization (App-V) package.
Install the App-V 4.6 client on the tablets.
B. Deploy the application as a published application on the Remote Desktop server.
Create a Remote Desktop connection on the tablets.
C. Install the application on a local drive on the tablets.
D. Install the application in a Windows To Go workspace.
E. Install Hyper-V on tablets.
Install the application on a virtual machine.
F. Publish the application to Windows Store.
G. Install the application within a separate Windows 8 installation in a virtual hard disk (VHD) file.
Configure the tablets with dual boot.
H. Install the application within a separate Windows 8 installation in a VHDX file.
Configure tablets with dual boot. Answer: F QUESTION 186
You support desktop computers and tablets that run Windows 8 Enterprise.
All of the computers are able to connect to your company network from the Internet by using DirectAccess.
Your company wants to deploy a new application to the tablets.
The deployment solution must meet the following requirements:
- The application is not accessible if a user is working offline.
- The application is isolated from other applications.
- The application uses the least amount of disk space.
You need to deploy the new application to the tablets.
What should you do? A. Deploy the application as an Application Virtualization (App-V) package.
Install the App-V 4.6 client on the tablets.
B. Deploy the application as a published application on the Remote Desktop server.
Create a Remote Desktop connection on the tablets.
C. Install the application on a local drive on the tablets.
D. Install the application in a Windows To Go workspace.
E. Install Hyper-V on tablets.
Install the application on a virtual machine.
F. Publish the application to Windows Store.
G. Install the application within a separate Windows 8 installation in a virtual hard disk (VHD) file.
Configure the tablets with dual boot.
H. Install the application within a separate Windows 8 installation in a VHDX file.
Configure the tablets with dual boot. Answer: B QUESTION 187
You support desktop computers and tablets that run Windows 8 Enterprise.
All of the computers are able to connect to your company network from the Internet by using DirectAccess.
Your company wants to deploy a new application.
The deployment solution must meet the following requirements:
- The application does not utilize the company server infrastructure.
- The application is isolated from other applications.
- The application uses the least amount of disk space possible on a solid-state drive (SSD) on the tablets.
- The application utilizes the least amount of network bandwidth.
You need to deploy the new application to the tablets. What should you do? A. Deploy the application as an Application Virtualization (App-V) package.
Install the App-V 4.6 client on the tablets.
B. Deploy the application as a published application on the Remote Desktop server.
Create a Remote Desktop connection on the tablets.
C. Install the application on a local drive on the tablets.
D. Install the application in a Windows To Go workspace.
E. Install Hyper-V on tablets.
Install the application on a virtual machine.
F. Publish the application to Windows Store.
G. Install the application within a separate Windows 8 installation in a virtual hard disk (VHD) file.
Configure the tablets with dual boot.
H. Install the application within a separate Windows 8 installation in a VHDX file.
Configure tablets with dual boot. Answer: D
Explanation:
Windows To Go is not a late-night drive-through offering at the local Microsoft Store.
Rather, its a feature in the Windows 8 Enterprise operating system that allows you to start a Windows 8 image (a Windows To Go workspace) from an external USB drive.
You can start a Windows To Go workspace on most computers that meet the Windows 7 or Windows 8 certification requirements, regardless of the operating system currently running on them.
http://technet.microsoft.com/en-us/windows/jj874386.aspx 2 QUESTION 188
You administer laptop and desktop computers that run Windows 8 Enterprise in an Active Directory domain.
Your company has purchased a subscription to Windows Intune.
You plan to install Intune Endpoint Protection on all computers.
Some of the computers also have another antimalware application installed.
You need to ensure that only the Intune Endpoint Protection application is running on all computers.
What should you do? A. Configure the Enable Realtime Protection policy to Yes.
B. Configure the Enable Endpoint Protection policy to Only on computers that are unprotected
when Endpoint Protection is installed.
C. Configure the Enable Endpoint Protection policy setting to Yes.
D. Configure the Enable Endpoint Protection policy setting to No. Answer: C QUESTION 189
Your company has purchased a subscription to Windows Intune.
You use Windows Intune to automatically deploy Windows updates.
You create an automatic approval rule in Windows Intune but notice that previously existing updates are not deployed.
You need to ensure that all previously existing updates are automatically approved.
What should you do? A. Run the approval rule.
B. Edit the schedule for the automatic approval rule.
C. Create and deploy a policy that uses the recommended settings in the Windows Intune Center
Settings template.
D. Create and deploy a custom policy in the Windows Intune Center Settings template. Answer: A QUESTION 190
You administer computers that run Windows 8 Pro.
The desktops have the Application Virtualization (App-V) client installed.
Multiple App-V applications are published on the network.
A user reports that it is taking a long time to launch App-V applications on his computer.
You discover that the user has a roaming profile on the computer.
You need to minimize the time that is required for the user to start App-V applications on the computer.
What should you do? A. Change the user profile to Super-Mandatory.
B. Change the location of the App-V client cache file on the computer.
C. Increase the size of the App-V client cache on the computer.
D. Change the user profile to Local. Answer: C
Explanation:
How to Change the Size of the FileSystem Cache
Reference: http://technet.microsoft.com/en-us/library/cc843780.aspx 3
You can change the size of the FileSystem cache by using the command line.
This action requires a complete reset of the cache, and it requires administrative rights.
To change the size of the FileSystem cache
Set the following registry value to 0 (zero):
HKEY_LOCAL_MACHINESOFTWAREMicrosoftSoftGrid4.5ClientAppFSState
Set the following registry value to the maximum cache size, in MB, that is necessary to hold the packagesfor example, 8192 MB:
HKEY_LOCAL_MACHINESOFTWAREMicrosoftSoftGrid4.5ClientAppFSFileSize
Restart the computer.
Braindump2go New Updated 70-689 Exam Dumps are Complete Microsoft 70-689 Course Coverage! 100% Real Questions and Correct Answers Guaranteed! Updated 70-689 Preparation Material with Questions and Answers PDF Instant Download: 
http://www.braindump2go.com/70-689.html
|