[2017-New-Version]Exam 400-251 VCE and PDF Dumps 425q Free Offered by Braindump2go[337-353]
2017 March New | CCIE 400-251 Exam Dumps with PDF and VCE Free Updated in www.Braindump2go.com Today!
1.|2017 Version 400-251 Exam Dumsp (PDF & VCE) 425Q&As Download:
http://www.braindump2go.com/400-251.html
2.|2017 Version 400-251 Exam Questions & Answers Download:
https://1drv.ms/f/s!AvI7wzKf6QBjgkdzKmReEoqH8Ov6 QUESTION 337
Which two statements about SCEP are true? (Choose two) A. CA servers must support GetCACaps response messages in order to implement extended functionality
B. The GetCRL exchange is signed and encrypted only in the response direction.
C. It is vulnerable to downgrade attacks on its cryptographic capabilities
D. The GetCert exchange is signed and encrypted only in the response direction.
E. The GetCACaps response message supports DES encryption and the SHA-128 hashing algorithm. Answer: AC QUESTION 338
Which two events can cause a failover event on an active/standby setup? (Choose two.) A. The active unit experiences interface failure above the threshold.
B. The unit that was previously active recovers.
C. The stateful failover link fails.
D. The failover link fails.
E. The active unit fails Answer: AE QUESTION 339
Which two statements about the MACsec security protocol are true? (choose two.) A. Stations broadcast an MKA heartbeat that contains the key server priority
B. The SAK is secured by 128 bit AES-GCM by default
C. When switch-to-switch link security is configured in manual mode, the SAP operation mode must be set to GCM
D. MACsec is not supported in MDA mode.
E. MKA heartbeats are sent at a default interval of 3 seconds. Answer: AB QUESTION 340
Which two options are benefits of network summarization? (Choose two.) A. It can summarize discontiguous IP addresses.
B. It can easily be added to existing networks
C. it can increase the convergence of the network
D. It reduces the number of routes
E. It prevents unnecessary routing updates at the summarization boundary if one of the routes in the summary is unstable. Answer: DE QUESTION 341
Refer to the exhibit. Which meaning of this error message on a Cisco ASA is true?
 A. The route map redistribution is configured incorrectly.
B. The default route is undefined.
C. A packet was denied and dropped by an ACL.
D. The host is connected directly to the firewall Answer: B QUESTION 342
Which two statements about uRPF are true? (Choose two.) A. The administrator can configure the allow-default command to force the routing table to use only the default route
B. It is not supported on the Cisco ASA security appliance.
C. The administrator can configure the ip verify unicast source reachable-via any command to enable the RPF check to work routing groups.
D. The administrator can use the show cef interface command to determine whether uRPF is enabled
E. In strict mode, only one routing path can be available to reach network devices on a subnet Answer: DE QUESTION 343
Which type of header attack is detected by Cisco ASA basic threat detection? A. connection limit exceeded
B. denial by access list
C. failed application inspection
D. bad packet format Answer: D QUESTION 344
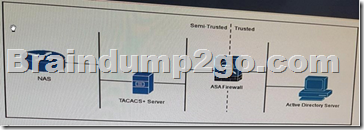
Refer to the exhibit. A user authenticates to the NAS, which communicates to the VACACS+ server authentication. The TACACS+ SERVER Then accesses the Active Directory Server through the ASA firewall to validate the user credentials.
Which protocol-port pair must be allowed access through the ASA firewall?
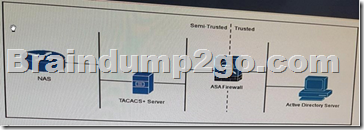 A. SMB over TCP 455
B. DNS over UDP 53
C. LDAP over UDP 389
D. global catalog over UDP 3268
E. TACACS+ over TCP 49
F. DNS over TCP 53 Answer: C QUESTION 345
Which WEP configuration can be exploited by a weak IV attack? A. When the static WEP password has been stored without encryption
B. When a per-packet WEP key is in use
C. When a 64-bit key is in use
D. When the static WEP password has been given away
E. When a 40-bit key is in use
F. When the same WEP key is used to create every pack Answer: E QUESTION 346
Which two statements about Botnet Traffic Filter snooping are true? (Choose two) A. It requires DNS packet inspection to be enabled to filter domain names in the dynamic database.
B. It requires the Cisco ASA DNS server to perform DNS lookups.
C. It can inspect both IPv4 and IPv6 traffic.
D. It can log and block suspicious connections from previously unknown bad domains and IP addresses
E. It checks inbound traffic only
F. It checks inbound and outbound traffic. Answer: AF QUESTION 347
Which three statements about SXP are true? (Choose three ) A. It resides in the control plane, where connections can be initiated from a listener
B. Packets can be tagged with SGTs only with hardware support
C. Each VRF supports only one CTS-SXP connection
D. To enable an access device to use IP device tracking to learn source device IP addresses.
DHCP snooping must be configured.
E. The SGA ZBPF uses the SGT to apply forwarding decisions
F. Separate VRFs require different CTS-SXP peers, but they can use the same source IP addresses. Answer: ABC QUESTION 348
Which file extensions are supported on the Firesight Management Center 3.1 file policies that can be analyzed dynamically using the Threat Grid Sandbox integration? A. MSEXE , MSOLE2 , NEW-OFFICE ,PDF
B. DOCX , WAV , XLS , TXT
C. TXT , MSOLE2 , WAV, PDF
D. DOC, MSOLE2, XML, PDF Answer: A QUESTION 349
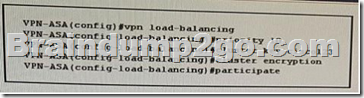
Refer to the exhibit You applied this VPN cluster configuration to a Cisco ASA and the cluster failed to form How do you edit the configuration to correct the problem?
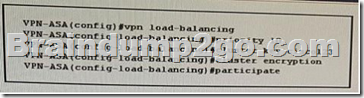 A. Define the maximum allowable number of VPN connections.
B. Define the master/slave relationship.
C. Configure the cluster IP address.
D. Enable load balancing. Answer: C QUESTION 350
Which effect of the crypto pki authenticate command is true? A. It sets the certificate enrollment method.
B. It retrieves and authenticates a CA certificate.
C. It configures a CA trust point.
D. It displays the current CA certificate. Answer: B QUESTION 351
Which effect of the ip nhrp map multicast dynamic command is true? A. It configures a hub router to automatically add spoke routers to the multicast replication list of the hub
B. It enables a GRE tunnel to operate without the IPsec peer or crypto ACLs.
C. it enables a GRE tunnel to dynamically update the routing tables on the devices at each end of the tunnel
D. It configures a hub router to reflect the routes it learns from a spoke back to other spokes through the same interface Answer: A QUESTION 352
Which statement about VRF-aware GDOI group members is true? A. IPsec is used only to secure data traffic.
B. The GM cannot route control traffic through the same VRF as data traffic
C. Multiple VRFs are used to separate control traffic and data traffic
D. Registration traffic and rekey traffic must operate on different VRFs Answer: A QUESTION 353
Refer to the exhibit. Which data format is used in this script?
 A. API
B. JavaScript
C. JSON
D. YANG
E. XML Answer: E
!!!RECOMMEND!!! 1.|2017 Version 400-251 Exam Dumsp (PDF & VCE) 425Q&As Download:
http://www.braindump2go.com/400-251.html
2.|2017 Version 400-251 Study Guide Video:
YouTube Video: YouTube.com/watch?v=YaNeWF28hfc 1
|